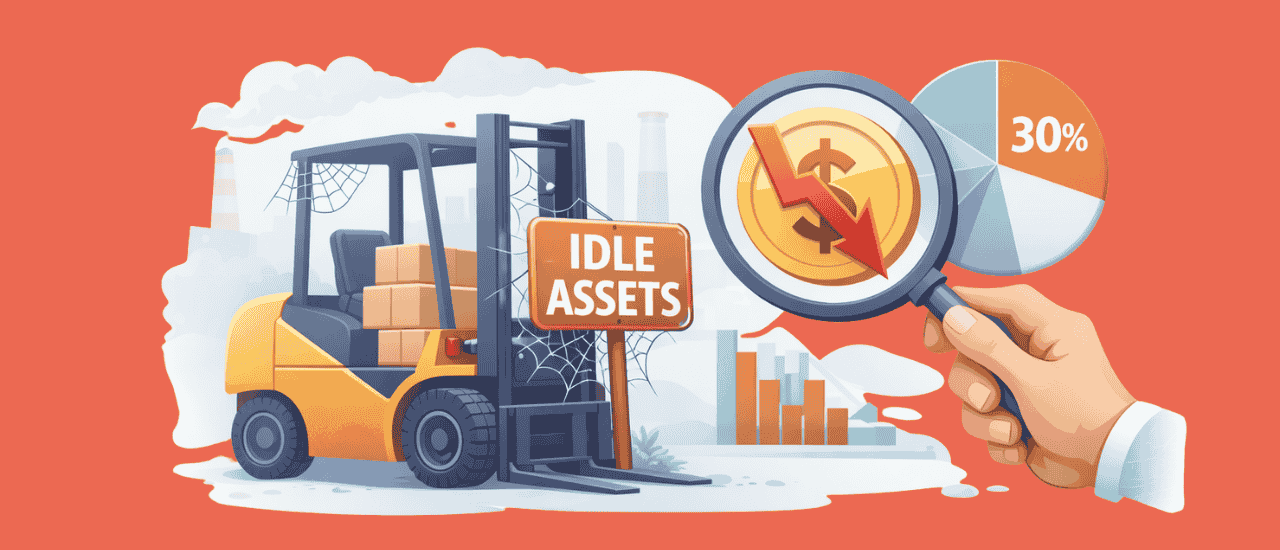
Imagine while the maintenance team working on some work order and they require a specific type of equipment, but they do not find it. Now the work is halted, and everyone has started looking for this required equipment. But they do not find it. These types of scenarios are quite common in all sectors. Now either asset theft occurred, or someone placed an asset in the wrong place. From the construction industry to the education sector, from manufacturing units to the oil & gas industry, asset theft is quite common.
Asset theft is a huge problem in all industries. Organizations must address it otherwise they will lose lots of assets along with that crucial information as well.
Why Does Asset Theft Occur?
Asset theft occurs because no one pays attention to those assets and suspicious people know about them. Assets are stolen because people know they can easily sell fortune can be made easily and assets are stolen for personal use as well. According to Finances Online, “95% of businesses encounter problems with employee theft.”
What Are the Consequences When an Asset or Device Theft Takes Place?
When a device or asset is lost, we not only lose equipment but with the device, we also lose valuable information.
Recommend To Read: What Are the Major Techniques for Effective Asset Management?
According to Statista, “the consequences of device theft or loss according to internet users worldwide as of June 2015. During the survey period, 25 percent of internet users reported that they permanently lost valuable personal assets such as photos, videos, etc. as a consequence of the theft or loss of a device.”
Below we have discussed consequences when an asset or device theft or misplacement occurs:

1. Personal information leakage
Lots of time it has been seen that employees put their information in the devices. When the device is stolen then sensitive information is leaked especially when it is in the wrong hands. Financial details stored at the device were stolen.
2. Account Hacking
To save time, lots of employees put their username and password on "Remember Me" mode. So that login time can be saved, and work can be done delivered efficiently. However, when device theft occurs, this type of event only leads to more destruction as any user can easily login.
There are several scenes in which after device theft organizations suffered from account hacked and the purpose behind asset theft is retrieving sensitive business information through account hacking.
3. Cannot Afford to Replace the Device
Some devices are so costly that replacing them with another one is not an option for organizations. As they do not have much of a budget to spend on other equipment or replace it with some other equipment. That is why it is important to take care of the device.
4. Permanently Lost Valuable Data
With asset theft, data loss also occurs and lots of valuable information is gone along with device. For instance, photos, videos, contacts, etc. Especially when data backup is not taken.
That is why it is always important to keep your data on cloud technology & backup must be taken regularly so that impact of theft can be minimized as much as possible.
5. Daily Operation Hindrance
Some devices such as mobiles or tablets are so important as they contain sensitive business information. If they are misplaced or stolen, then a work hindrance occurs. These types of devices have a lot of dependencies as they contain lots of valuable business information and daily operations inputs are not done accurately as these devices are lost.
When this type of scenario occurs, it only leads to decreased productivity as no one is prepared for these types of situations.
These are only a few of the consequences when device theft occurs. It is important to eliminate asset theft & asset misplacement and it shall be not taken lightly.
How to Avoid Asset Theft and Asset Misplacement?
Asset theft and misplacement can be avoided with asset tagging and asset tracking software. When you combine these two methods you can easily avoid asset theft.
An asset tag is an effective solution as it provides an accurate location of the asset. When you utilize it with asset tracking software you do not only avoid asset theft, but you can also retrieve crucial information.
Each asset tag has a unique identification number that provides the accurate location of each asset. When you utilize asset tracking software, you can gather more vital information and boost asset productivity as well.
Conclusion
Asset theft is not a small issue, and it has been a problem for a long time. Therefore, actions must be taken to eliminate device, asset theft, and asset misplacement issues. That is why investing in asset management software is essential for business.
It can help you from saving assets from theft and provide security to the asset. Furthermore, it provides several other benefits as well to your business that will give an extra edge to your business that will help you in growing your business.
Frequently Asked Questions (FAQs)
What Are the Other Techniques for Saving Assets from Theft and Misplacement?
Other techniques for saving assets from theft and misplacement are given below:
1. Utilizing surveillance camera.
2. A thorough check of employees when they enter or leave the premises of the organization.
3. Alarm system.
4. Biometric system.
What Are the Benefits of Asset Management Software?
The benefits of asset management software are given below:
1. Asset lifecycle management.
2. Scheduling asset maintenance process.
3. Eliminating ghost assets.
4. Better compliance and fast asset auditing.
5. Increased productivity.
6. Decreased maintenance expenses.
7. Better return on investment (ROI).
Does This Software Come with Cloud Technology?
Yes, this software comes with cloud technology. Cloud technology enables you to access data from anywhere across the world and it saves data online. Therefore, you do not have to worry if assets are misplaced, or theft occurs. Furthermore, data security is also provided by the cloud service provider.

































.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)

.svg)




.webp)
.webp)





























.webp)